 Most of you might have enabled wireless encryption, which is only one of the 6 steps mentioned in this article to make your wireless network safe and secure from hackers. The screenshots mentioned below are from Linksys wireless router. But, you’ll find similar options for all the 6 steps mentioned below in wireless routers from any other vendors.
Most of you might have enabled wireless encryption, which is only one of the 6 steps mentioned in this article to make your wireless network safe and secure from hackers. The screenshots mentioned below are from Linksys wireless router. But, you’ll find similar options for all the 6 steps mentioned below in wireless routers from any other vendors.
Apart from these 6 steps to secure your wireless router, also make sure your wireless router firmware is up-to-date. Refer to our 4 easy steps to upgrade linksys wireless router firmware article for detailed instructions on how to upgrade your router firmware.
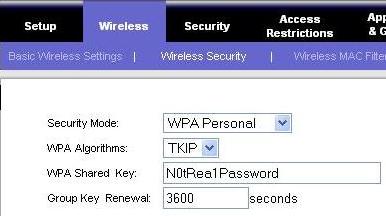
1. Enable Encryption
Let us start with the basics. Most of the wireless router has the encryption disabled by default. Make sure to enable either WPA or WPA2 wireless encryption. Click on Wireless -> Wireless Security , to enable the encryption and assign a password as shown in Fig-1. Following are the different wireless encryption options available.
- WEP (Wired Equivalent Protection) 64-bit and 128-bit: WEP is an old wireless encryption standard. Never use WEP encryption, which can be hacked within seconds.
- WPA (Wi-Fi Protected Access): WPA-PSK is also refered as WPA-Personal. This is a new version of wireless encryption standard and more secure than WEP. Most of the wireless adapters on your laptop will support WPA.
- WPA2: This is the latest wireless encryption standard that provides the best encryption. Always use WPA2, if both your wireless router and laptop wireless adapter supports it.
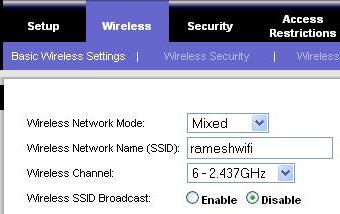
2. Change the SSID name
SSID (Service Set Identifier) refers to the name of your wireless connection, that you see on the “Available Wireless Connections” list from your laptop while connecting. Changing the wireless name itself doesn’t offer any protection, but usually discourages a hacker, as they know that you’ve taken some steps to secure your wireless connection. Click on Wireless -> Basic wireless settings -> Change the “Wireless Network Name (SSID):”, as shown in the Fig-2.
3. Disable SSID broadcast
You can avoid your wireless name from getting displayed on “Available Wireless Connections” on all your neighbors laptop. This can be done by instructing the wireless router not to broadcast the name to everybody. Once you’ve disabled the SSID broadcast, the first time when someone wants to connect to your wireless network, you need to provide the name to them. Click on Wireless -> Basic wireless settings -> Click on the Disable radio-button next to “Wireless SSID Broadcast”, as shown in Fig-2.
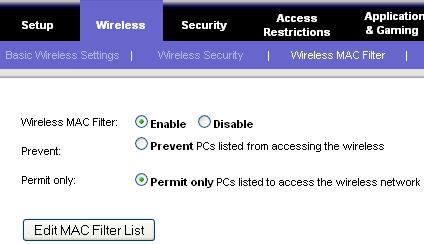
4. Enable MAC filtering
Even after you have performed the above item#1 – #3, a very determined hacker may still get access to your network. The next security step is to allow wireless access only to your trusted laptops, by allowing wireless connection only to known MAC address. MAC (Media Access Control) address is an unique identifier attached to most network adapters. In this case, this should be the unique identifier of your laptop wireless adapter. On Linux, do ifconfig from the command prompt to get wireless hardware address. On windows, do ipconfig /all from the command prompt to identify the MAC address as shown below.
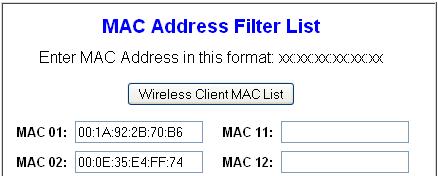
C:>ipconfig /all Ethernet adapter Wireless Network Connection: Connection-specific DNS Suffix . : socal.rr.com Description . . . . . . . . . . . : Dell Wireless 1390 WLAN Mini-Card Physical Address. . . . . . . . . : 00:1A:92:2B:70:B6
Click on Wireless -> Wireless MAC filter -> Click on Enable radio-button next to “Wireless MAC filter” -> Click on “Permit only PCs listed to access the wireless network” radio-button, as shown in Fig-3.
Click on Edit MAC filter list and add the MAC address of your laptop to this list. If you want to allow access to more than one laptop, add the MAC address of all the laptops to this list as shown in Fig-4 and click on “Save Settings”.
5. Change password for Web Access
The default password for wireless web access are the same for the specific model of a wireless router assigned by the manufacturer. Change the default password of the wireless router web access to a strong password. Follow The Ultimate Guide For Creating Strong Passwords to choose a strong password. Click on Administration -> Management, to change the password as shown in Fig-5 below.
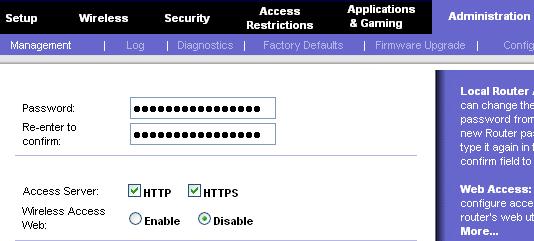
Fig-5 Change password and disable wireless web access
6. Disable administrative access through web
As a final step, make sure to disable web administrative access through wireless. Once you do this, to make any configuration changes to the wireless router, you can always use ethernet cable connection from your laptop to configure the wireless. Click on Administration -> Management -> Disable radio-button next to “Wireless Access Web”, as shown in Fig-5 above.
If you liked this article, please bookmark it on del.icio.us and Stumble It.






Comments on this entry are closed.
You are couple of weeks late in posting this Ramesh 😆 Last month I bought a new LinkSys router and had tough time to get it work with my Airtel broadband connection. Finally, I was successful, though I need to once again go through the steps mentioned here for better security.
Cheers,
Ajith
A good idea for people that haven’t enough info about your wireless router. Only a recomendations, add like step 0 the change of standard administrative user/password for router tipically like admin/admin or so on.
Thanks for you contributions. Manuel.
MAC filtering is useless. The only protection against someone trying to use Your wireless network is encryption.
My preferred encryption for my home network is similar.
I do not use anything like wep or wpa
I use mac filtering
I do display my ssid
I turn off DHCP and use specified IP addresses
If you do choose to go the same route as I, I recommend using a range that is very uncommon. Dont use 192.168.x.x, or 172.x.x.x or anything like that, make something unique like 39.182.x.x That way people in your area are saying to themselves “Sweet! and unsecured network!” and while they’re trying, they arent getting past your mac filtering, and would have trouble determining your gateway and dns as well
“Experienced” users will probably have some nay to say about my set up, but I don’t protect against people who know how to get around my network, cause chances are if they want in, they’ll get in no matter what encryption you have. I protect against the downstairs neighbor who decides they don’t want to pay for internet and want to steal my 18Mbps connection instead
MAC Filtering is completely useless, anyone can change their MAC address (it’s in the properties for your network card under advanced).
You shouldn’t disable broadcasting SSID either. This link from Microsoft explains why: http://technet.microsoft.com/en-us/library/bb726942.aspx The main problem is this: When you connect your laptop to a non broadcasting SSID, and set it up to auto reconnect – then every time you turn your laptop on, it will broadcast out that SSID name “HEY *SSID* are you there!!?”. This becomes a problem say, when you go to the Airport and bootup your laptop it will broadcast that SSID. Now all a hacker has to do is setup *his* laptop as an Ad-Hoc network with the same SSID that you normally connect to – your laptop will connect to it thinking it’s the usual “home network SSID”. The hacker could setup his Ad-Hoc to relay traffic out to the Internet so you may think you have a good, live Internet connection – meanwhile the hacker is capturing all the traffic including usernames and passwords while you browse the Internet.
Lets face it wireless can always be hacked, but the best way to look at it is the same way as you car. Park it next to a better looking one or one with the windows down and yours will probably be left. Same with your wifi turn on all the options you have and most hackers will go for an easier option.
What anon said. Most people aren’t going to go through the time and effort to leech your wireless network if there are easier targets around. It’s just not worth the trouble.
@Ian,
Thanks for the explanation about SSID broadcast and link to the excellent article on this subject from Microsoft site.
@Corey,
Turning of DHCP and using static ip is very good idea. But, I would still recommend that you keep it encrypted on top of what you’ve already done.
@tommy,
I agree that MAC filter are not secure and can be spoofed very easily. But, like other’s have mentioned, a hacker may not be interested in targeting your wireless, if you have taken steps to secure it, as the hacker may easily find other wireless network that are less secure.
@Ajit, @Manual, @Anon, @Paul,
Thanks a lot for posting your comments. I sincerely appreciate it.
When will people learn. #2-4 and Corey H’s suggestion are completely useless for security and here’s why.
If you don’t have WPA and a good long passphrase, any noob can download airsnort and:
1) Find your SSID, hidden or not.
2) Find the MAC addresses of all your wireless devices and spoof any one.
3) Find your gateway IP no matter what IP range you use.
Trust me, I’ve done this many times for penetration testing. #2-4 will only make it much harder for you to add new devices to your network they offer no security beyond WPA whatsoever. In fact, they add a false sense of security which is worse. As long as you have a good WPA passphrase it doesn’t matter if your neighbors know all the rest of the info, it’s useless.
To Corey, what you’re doing is not only not a good idea, it breaks IP routing. You can’t just choose a random address range. 192.168 etc. are used for a reason. Those are private IP ranges. If you choose a random IP range that happens to belong to Google, you won’t be able to access Google since your IP routing table won’t use the gateway for that range. Also, it’s trivial for someone to determine your gateway address if they’re already connected to your WiFi. Lastly, they don’t need to know YOUR DNS addresses, they can use ANY DNS address.
To those who say “I don’t care if someone uses my connection”, have you thought about this: They could be downloading MP3s, movies, porn etc. which can land you in jail and cost you tens of thousands in legal fees. They could also be seeding viruses, launching DDoS attacks or even capturing your emails and gathering information for a social engineering attack.
No matter what, wireless isn’t secure. Whether you keep sensitive files, and/or care about someone hacking it is what you should be concerned about. As far as people saying, “Hackers will go for easier targets…” perhaps thats true. However, I like the challenge of getting into a tougher target. If the target is super secure, they might have more information on the network, or have the higher grade internet connection.
The information here is helpful, but won’t prevent those with a little more knowledge about how to go about getting the end result. However it should prevent some of the new hackers from succeeding.
@T
I disagree. A good wireless connection can be as secure as a wired connection (possibly more secure if your wired LAN does not require authentication). If WPA is compromised it’s either a because of a weak passphrase or user who was conned to revealing credentials, not the technology itself.
If you’ve been able to break a WPA2-enterprise (802.1x) with a pseudo-random passphrase of 16 or more characters then I’d really like to know about it.
The fact is if you broadcast it (as in ANY wireless signal) it can be hacked, no if’s, and’s, or but’s about it. I have been an engineer for 10 years, having spent a lot of time working with network security, and nothing, I mean nothing, on earth is unhackable (unless it is physically unplugged from an internet connection). The best you can do is limit the number of people that have the skillset, that is, you can make it hard enough that only a talented, experienced hacker can get in, but even then it is only a matter of time.
@Kamikaze, @T, @Steve,
Thanks for posting your detailed comment on the wireless security, to keep this discussion very informative.
No more free internet for neighbors 😀 Thanks for posting this useful info.
Great article, Ramesh. I found this site via Stumbleupon. I love the content. Keep up the good work.
I just want to ask. Where did you get your blog theme and what is its name?
Thank you
Great tips featured here!
I’m currently doing just encryption at the moment, all that other stuff I will look into and hopefully it will help our wireless network.
I have one. Install DD-WRT, then do what it said to do.
Well, folks, you have to do something. I do all Ramesh says. I never auto connect via wireless.
Recently a laptop of mine was retired from daily use and I loaded Linux on it and it is what I connected my router to. Everything from the net goes through the Linux box and then to the other systems. I put two gig network cards in it. The WAN and LAN are separated.
Somebody is going to have to go through a hell of a lot to find I have nothing for them.
I agree with Steve that any wireless signal can be sniffed, and possible intercepted, manipulated etc. even your dish for the TV. For most people having to secure their own home wireless network, i believe the following setup be sufficient
router:
1. hide your ssid broadcasts
2. use wpa2 encryption with a strong password you can use a “random” wpa key generator from the internet (search google for wpa key generator”. choose a 63 char.
3. use mac filtering
pc/laptop/mobile/whatever:
1. disable auto reconnect if disconnected
2. select only allow connection to access points
btw, are there any wireless “defense” auto checker programs out there for windows? there are so many tools available for sniffing, hacking purposes…Where are the defense!? 😀
how do you protect yourself against deauths!? except dont auto reconnect to your network…are there other ways?
I will remind you all of an old joke. Two hikers are tramping through the woods, and and angry bear comes around a bend and starts after them. The first guy starts to run, then looks back and see’s the 2nd guy changing out of his hiking boots into his jogging shoes. “What are you doing!!!?? We have to get the f*ck outa here! Run!!!” The second guy says, while finishing the lace on his shoe says, “I don’t have to outrun the bear, I just have to outrun you.”
True in all things criminal. Make yourself a more difficult target, and unless you’ve posted on the internet that your network has something valuable on it, any hacker is going to look at your non-SSID-broadcasting, WPA2 encrypted, MAC-filtering network and just move on to the guy down the street with the linksys default settings. Locks only keep out honest people, but if you make it complicated for them, you’ll be fine, probably. Criminals, on the average, are lazy. That’s why they’re criminals. They don’t like work.
@Morgan,
Thanks for the reference to DD-WRT. For those who are interested, DD-WRT is a free Linux-based firmware for wireless router.
@Gene0,
For this blog, I started with the Networker Theme and made significant changes to it.
@Bill,
Telling story is the best way to explain something. You’ve just proved it. Thanks.
@thenetguruz, fredex, anon,
Thanks for your comments. I really appreciate it.
Just to take this discussion further, you may want to follow-up with other tips for securing home computer systems. Security the wireless connection is a good first step, though it is only one way people get hacked. Home users should also ensure they secure their web-browser, OS, applications, etc. Here are some further tips if people are interested:
http://www.mbridge.com/security_advice_home_users.html
Thanks for the article. It was helpful.
Thanks for that, I now have secure Wi Fi..
Use WPA2-Enterprise, if possible (requires RADIUS). Lower the
output power of the device, and never keep any personal or
financial information on the laptop. I use my wired PC for that.
Finally, have the router turn off wireless capabilities when you’re
not around, and have a system log (syslog) running. If using
WPA2 Ent. , change the key hourly. If using WPA2-Personal,
use a 63 character random key, and change this as often as
is tolerable (when I did use personal, my toleration level was
about every 3 days). On the laptop, if you must have personal
information on it, use encrypted file system or some other
file system encryption. This is good practice regardless of
whether it uses a wireless connection or not. Turn off auto-connect
on the laptop.
Do you have any idea how to unlock ADSL router that works only on some prefered connections?
I wish I found your post much earlier when I was setting up my wireless network. Would have saved me a lot of time. Going into my bookmarks for future reference.
@Jarav, Steve H
Thanks for your comment. I’m glad you found this article helpful and secured your wireless router.
@Cushman,
Changing wireless key frequently is a good idea. But, it may not be possible for most people to change it every 3 days for WPA-Personal encryption. May be once in a month is reasonable? — not from pure security point of view.
@Mohit,
I’m not sure what model of ADSL router you have. Some models don’t allow unlocking. I’ve seen few unlocked firmware for some ADSL routers floating around. The tricky part is that you’ve to find a way to put the unlocked firmware in the flash, as most firmware will detect any changes to the flash and will not allow it.
@Bruno,
Thanks for bookmarking this page. I appreciate it.
For those, who need to return, bookmark this page at del.icio.us for handy reference.
MAC filtering is useless. The only protection against someone trying to use Your wireless network is encryption.
Hy… thanks ramesh for this wonderful stuff.now secured my network with WPA2.Got struck in the middle ,but completed safely.Thanks again.
Mac address filtering is the best option in order to secure the network. As well as we may need to disable “wps” in router setup page. WPA PSK is suitable only for vista and above (i.e in Dlink and Belkin).
i would add number 7 which is, hold firmware on your router updated. it will to avoid exploit known security issues
Please provide “ids” for your “headers”. I’d like to directly link to “4. Enable MAC filtering”.
Dear Ramesh,
Thanks very much for explaining the essentials of securing wireless home routers so lucidly. You have indeed peformed a public service. Thanks again, my friend.
I want to change the name of the wireless network… where do I find “tool bar” that you show in the screen shots? How do I get to that?
Actually changing the SSID makes the encryption alot more secure since passwords are salted with it.
Ramesh,
I have read many of your articles and free stuff (really knowledge giving ones).
You could have also mentioned, how to get into this setup. I have now installed an MTNL broadband with wireless modem.
I have done these a 2 yr back when I was in chennai, but now fully forgotten this.
please if you could give me this one too.
Great article (s),
s.sivakumar
mumbai
98200 10728
Append _nomap to your SSID to prevent google from adding your WAP to their map, assuming you trust google to not map it if you do this.
Hi Ramesh!
You don’t know how you have opened my eyes and knowing that there is a possibility of me securing my home wireless. At first I didn’t know how this is done!.
good.
Hi Ramesh,
I love your site and your advice … but … the advice you give for securing the wireless router Linksys WRT54G is dead wrong.
http://www.thegeekstuff.com/2008/08/6-steps-to-secure-your-home-wireless-network/#respond
1. It ‘is’ a security measure to change the SSID but for a wholly different reason than what you suggested. Google “butterfly hash tables” for WPA2 encryption to see why.
2. Disabling SSID broadcast does almost nothing (sure, it helps a teeeny bit, but the SSID is always in the packet so it can be sniffed easily).
3. Same with MAC filtering.
4. Changing the password and restricting administrative access “are” good ideas!
Thanks again for the article – but please correct the misconceptions above.
good article
its simple way to protect your wifi………..
The 54Mbps Wi-fi G ADSL 2/2+ Modem Router (model TEW-436BRM) can be an all-in-one modem in addition to wifi g router.
No need to obtain a individual modem in addition to router. This kind of streamlined unit offers an ADSL 2/2+ modem wifi g router in addition to 4-port transition just about all in one merchandise.
Install OpenWRT, dude!
Rule no 6 is the most restrictive step to prevent any hackers from entering our network.Thanks for providing such a robust step, Sir.
Looking for securing my wi-fi connection I found these tips very useful. What about using a VPN?